Tag: Featured
-
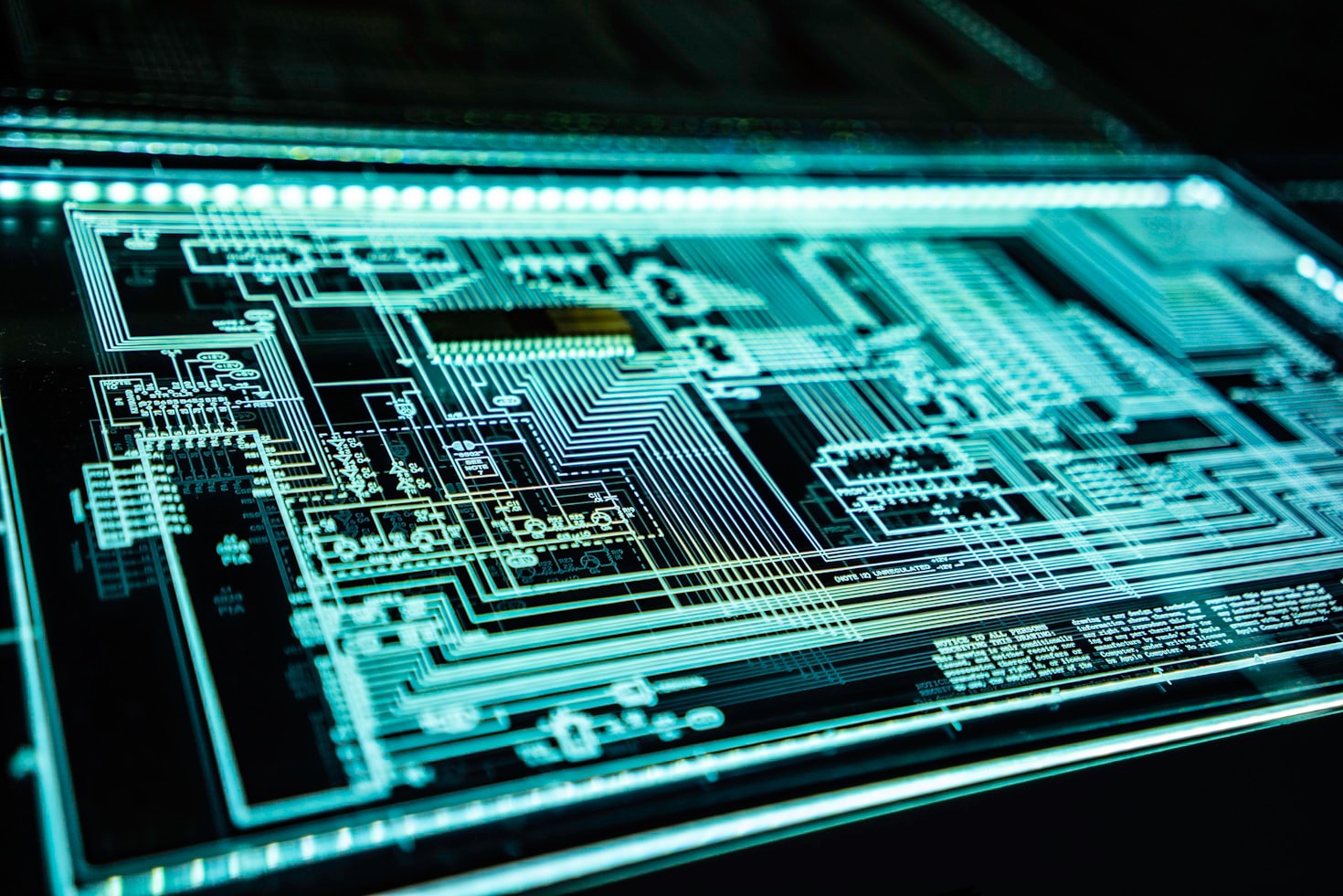
Cyber threats now cross borders effortlessly, fueled by geopolitical conflicts, advanced technology, and interconnected economies. In 2026, organizations face attacks from distant actors aiming to disrupt, steal, or extort. Prevention requires proactive strategies that anticipate these global risks and stop them early. Attackers operate from anywhere, using AI to craft convincing phishing, automate malware, or…
-
This paragraph serves as an introduction to your blog post. Begin by discussing the primary theme or topic that you plan to cover, ensuring it captures the reader’s interest from the very first sentence. Share a brief overview that highlights why this topic is important and how it can provide value. Use this space to…
-
This paragraph serves as an introduction to your blog post. Begin by discussing the primary theme or topic that you plan to cover, ensuring it captures the reader’s interest from the very first sentence. Share a brief overview that highlights why this topic is important and how it can provide value. Use this space to…
-
This paragraph serves as an introduction to your blog post. Begin by discussing the primary theme or topic that you plan to cover, ensuring it captures the reader’s interest from the very first sentence. Share a brief overview that highlights why this topic is important and how it can provide value. Use this space to…